OSINT used to take days. AI now does in seconds what used to require entire analyst teams. Here’s everything changing - and what it means for you.
Introduction: The Old OSINT Is Dead
Cast your mind back to 2019. An OSINT investigator tracking a person of interest had to:
- Manually search 30+ social media platforms one by one
- Download images and run them through reverse image tools by hand
- Cross-reference breach databases in separate tabs
- Read thousands of forum posts hoping to catch a pattern
- Build relationship maps in a spreadsheet
A skilled analyst could spend three full days building a basic profile. And they’d still miss things.
Today? That same investigation - using modern AI-powered OSINT tools - takes under an hour. In some cases, under five minutes.
AI significantly improves the speed, accuracy, and efficiency of OSINT investigations, helping professionals track threats, verify sources, and extract intelligence with minimal human intervention. The global OSINT market reflects this shift: valued at $5.02 billion in 2018, it is expected to grow to $29.19 billion by 2026, with a CAGR of 24.7%.
This isn’t incremental improvement. This is a complete paradigm shift. Let’s break down exactly how.
Part 1: What AI Actually Does Inside OSINT Tools
Before we look at specific tools and scenarios, let’s understand the core ML capabilities that are powering this revolution.
1.1 Natural Language Processing (NLP)
Natural Language Processing enables AI to extract intelligence from text-based sources, such as news articles, social media posts, and leaked documents.
In practice, NLP allows tools to:
- Scan thousands of forum posts and flag only the relevant ones
- Extract named entities (people, places, organizations) automatically from unstructured text
- Detect sentiment shifts that might indicate threat escalation
- Match writing styles across pseudonymous accounts
Real Scenario: A threat intelligence analyst monitoring a far-right Telegram channel doesn’t read 10,000 messages manually. An NLP model ingests the channel in real time, flags posts mentioning specific targets, locations, or weapons — and generates a daily brief. What used to need a team of five now runs on one analyst’s laptop overnight.
1.2 Computer Vision & Image Intelligence
This is where AI has arguably made the biggest leap. The ability to convert images and video to natural language - which can be queried like a search engine - now exists. Tools can crawl troves of images and videos to detect guns, weapons, or even client logos.
What this means in practice:
- Upload a photo → AI identifies location from background details (buildings, signs, terrain)
- Run a face through a recognition engine → returns all public web matches in seconds
- Submit a video → AI transcribes audio, identifies speakers, flags suspicious objects

Computer vision models can now identify weapons, logos, geographic landmarks, and faces across millions of images in the time it would take a human to scan a single page.
1.3 Entity Resolution & Pattern Correlation
This one is subtle but enormously powerful. AI can be leveraged to correlate seemingly disparate user data sets - at scale and in real-time. Historically, determining that John Smith in Portsmouth isn’t John Smith in Portland would have taken an analyst hours. AI makes these queries a near-real-time exercise, with confidence scores and analysis at the click of a button.
1.4 Anomaly Detection
Machine learning models trained on normal behavioral baselines can flag when something is off:
- An account that posts 200 times a day (bot behavior)
- A domain registered 48 hours before a phishing campaign
- An IP that suddenly routes through 7 different countries
- A profile photo that reverse-searches to a stock image site
AI can spot patterns and inconsistencies that would be much harder to notice with the naked human eye.
Part 2: The AI-Powered OSINT Toolkit in 2026
Maltego + ML Models
Maltego is one of the most advanced AI-driven OSINT tools for intelligence gathering and digital forensics. It uses machine learning to map relationships between individuals, organizations, and domains and automates data collection from public and private OSINT sources.
Maltego excels in mapping connections between entities — individuals, organizations, IP addresses, or domains. It integrates with machine learning models for entity recognition and enables users to automate and visualize relationships.
# Maltego transform example — automated entity enrichment
# In the Maltego GUI, right-click any entity and run:
# "To Person [via Social Media Lookup]"
# "To Phone Number [via OSINT Sources]"
# "To Related Domain [via Certificate Transparency]"
# Maltego CE is free — download at maltego.comWhat it finds: Email addresses linked to a domain → social profiles linked to those emails → physical addresses from public records → associates and org charts.
SpiderFoot — Automated OSINT Orchestration

SpiderFoot is an open-source intelligence tool that aids security professionals, pentesters, and investigators in mapping a target’s attack surface. It offers 200+ modules that integrate with a variety of data sources and collects data on IP addresses, domain names, email addresses, and other relevant entities.
# Install SpiderFoot
pip3 install spiderfoot
# Launch web UI
python3 sf.py -l 127.0.0.1:5001
# Or run headless scan from CLI
python3 sfcli.py -s target@domain.com -t emailaddr -m sfp_hunter,sfp_linkedin,sfp_shodanSpiderFoot’s ML-enhanced modules can:
- Correlate an email address to 40+ data sources simultaneously
- Detect data breach exposure automatically
- Map infrastructure and hosting patterns
- Generate relationship graphs without manual input
Shodan + AI Queries
AI-powered tools like Shodan scan exposed devices, open ports, and unprotected servers to identify security risks.
# Shodan CLI — find exposed webcams in a specific country
shodan search "has_screenshot:true country:KE"
# Find exposed industrial control systems
shodan search "port:102 product:SIMATIC"
# AI-enhanced: Shodan Monitor sends real-time alerts when
# new assets matching your search appear — no manual polling
shodan alert create "org:TargetCompany"Real Scenario: A red team conducting pre-engagement OSINT against a financial firm used Shodan’s AI-enhanced monitoring to discover a forgotten dev server running an exposed Grafana instance - the same CVE that had been in the news three weeks prior. The client had no idea it existed. That single Shodan query opened the entire engagement.
Taranis AI — Automated Threat Intelligence
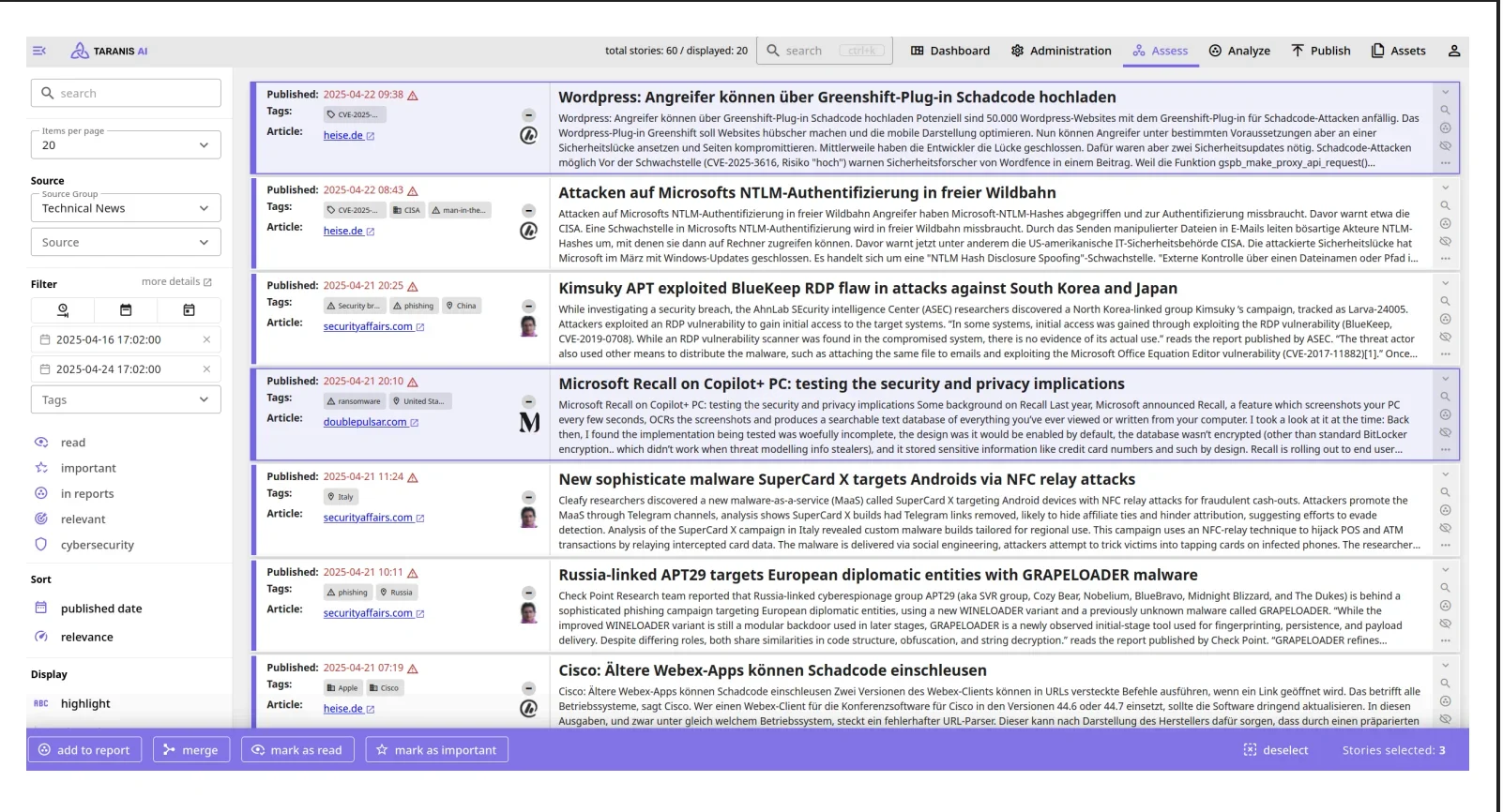
Taranis AI is an advanced OSINT tool leveraging artificial intelligence to revolutionize information gathering and situational analysis. It navigates through diverse data sources like websites to collect unstructured news articles, utilizing NLP to enhance content quality. Analysts then refine AI-augmented articles into structured reports.
What makes Taranis notable: it’s fully automated. Point it at a set of sources -news feeds, security blogs, government advisories, dark web forums - and it delivers structured, summarized intelligence briefings without human curation of raw data.
Recorded Future - Predictive Intelligence
Recorded Future combines machine learning and NLP to deliver actionable threat intelligence. The platform integrates with SIEMs and SOAR solutions for connected workflows.
The key word here is predictive. Recorded Future’s ML models don’t just describe what has happened - they flag indicators suggesting what’s about to happen. For example: monitoring chatter around a specific CVE across dark web forums and hacker Telegram channels, and alerting an org before exploits go public.
MiroFish — Swarm Intelligence & Social Prediction Engine
🔗 GitHub: github.com/666ghj/MiroFish ⭐ 32.3k + stars
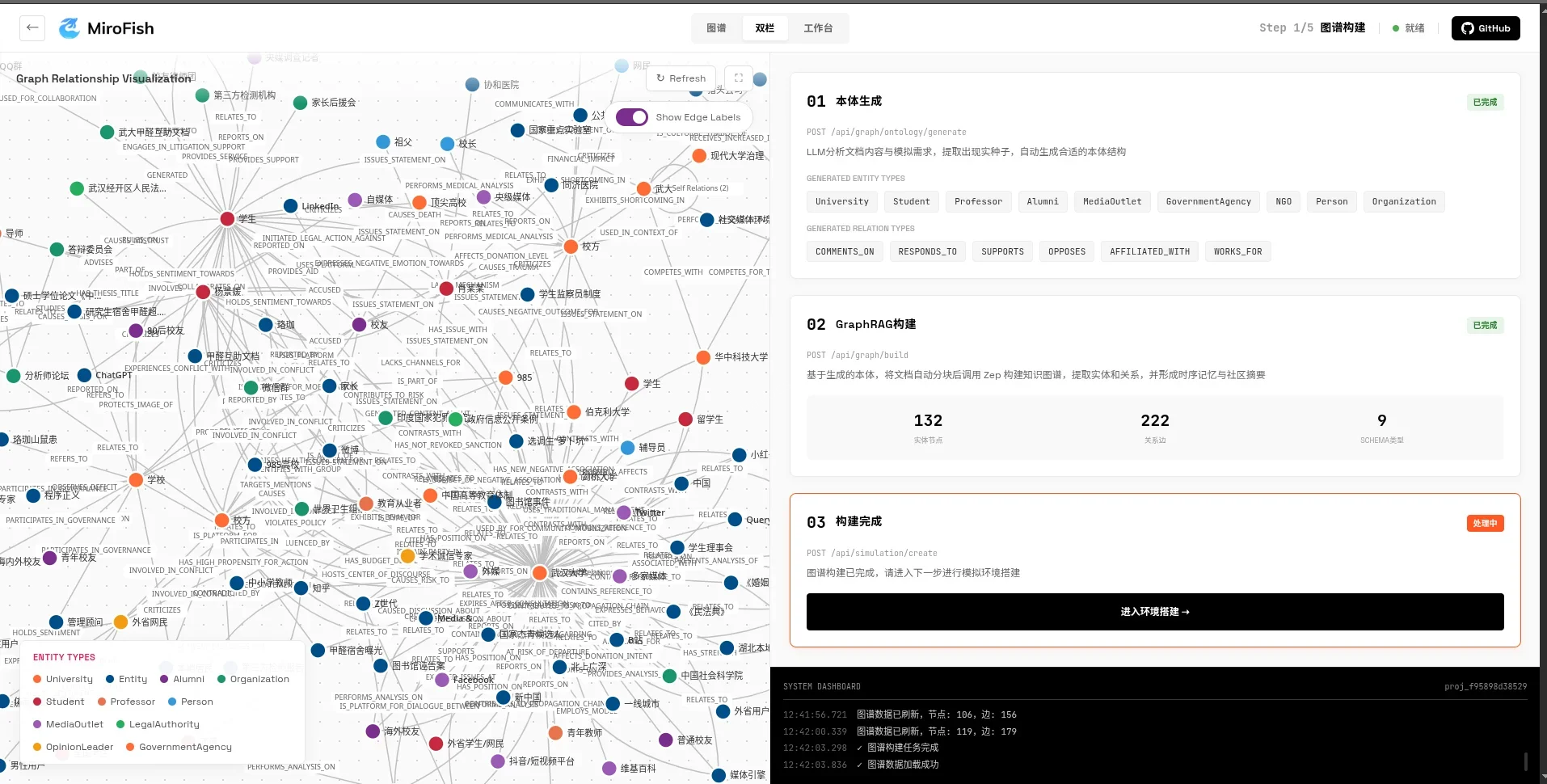
MiroFish is one of the most fascinating AI tools to hit the open-source intelligence space in 2026 - and most OSINT practitioners haven’t heard of it yet.
At its core, MiroFish is a multi-agent swarm simulation engine. You feed it a “seed” - a news article, a policy document, a financial report, a social media trend - and it constructs a high-fidelity digital parallel world. Inside that world, thousands of AI agents with individual personalities, long-term memories, and behavioral models interact autonomously. The engine then generates a structured prediction report of how that seed event will ripple through society.
Why it matters for OSINT:
Standard OSINT tools tell you what has happened or what is happening right now. MiroFish addresses a different question entirely: what is likely to happen next?
For investigators and analysts, that unlocks genuinely novel use cases:
| OSINT Use Case | How MiroFish Helps |
|---|---|
| Disinformation campaign analysis | Seed it with a false narrative - simulate how it spreads, who amplifies it, and where it peaks |
| Threat actor behavior forecasting | Model how a group responds to law enforcement pressure or public exposure |
| Public figure crisis prediction | Simulate the public reaction to a leak or scandal before deciding how to handle it |
| Election / influence operation mapping | Forecast social polarization based on specific messaging campaigns |
| Brand/reputation threat assessment | Run a simulated crisis to predict damage vectors and response windows |
# Quick Docker deploy — get MiroFish running locally in minutes
git clone https://github.com/666ghj/MiroFish
cd MiroFish
# Copy and fill in your API keys (.env.example has all required vars)
cp .env.example .env
# Edit .env: set LLM_API_KEY, LLM_BASE_URL, LLM_MODEL_NAME, ZEP_API_KEY
# Launch frontend (port 3000) + backend (port 5001) together
docker compose up -d
# Or run from source (Node 18+ and Python 3.11-3.12 required)
npm run setup:all # installs all dependencies
npm run dev # starts both servicesSeed input example — disinformation investigation:
Upload: a report documenting a coordinated health misinformation campaign
Prediction request (natural language):
"Predict how this narrative will evolve over the next 2 weeks across
Twitter, Telegram, and regional news outlets. Identify the likely
amplification nodes and the point at which mainstream media picks it up."
MiroFish output:
→ Structured prediction report with timeline
→ Network map of simulated amplifier agents
→ Estimated reach and sentiment curve
→ Recommended intervention windowsReal Scenario — applied OSINT:
A threat intelligence team tracking a hacktivist group used MiroFish to model how the group would react to a planned public attribution by a government agency. They seeded it with: the attribution press release draft, the group’s historical statements, and relevant geopolitical context.
The simulation forecast a retaliatory DDoS campaign targeting government infrastructure within 72 hours of publication - naming three specific agency domains as most likely targets based on agent behavioral modeling.
The government agency delayed publication by one week, hardened those three domains, and when the attribution finally dropped, the predicted DDoS came - but hit significantly hardened infrastructure. The threat was mitigated before it fully materialized.
💡 Bottom line: MiroFish doesn’t replace traditional OSINT tools — it extends them into the future tense. Where Maltego maps what is, and Recorded Future flags what’s emerging, MiroFish models what will be. Used together, they give an analyst a 360° temporal view: past, present, and predicted future.

MiroFish runs thousands of AI agents simultaneously, each with independent memory and behavior - modeling social dynamics the way weather systems model atmospheric pressure: from the ground up.
Pixalytica + Lenso.ai — AI Face & Image Intelligence
Pixalytica combines a facial recognition engine with AI-powered technology that gathers as much information as possible about a specific person. Starting from just an image, it delivers a complete report - including all face search matches - in under 20 seconds.
Lenso.ai also allows users to search for exact duplicates of an image, places shown in a photo, and similar or related images. Its Research Mode can find up to 10,000 image search results.
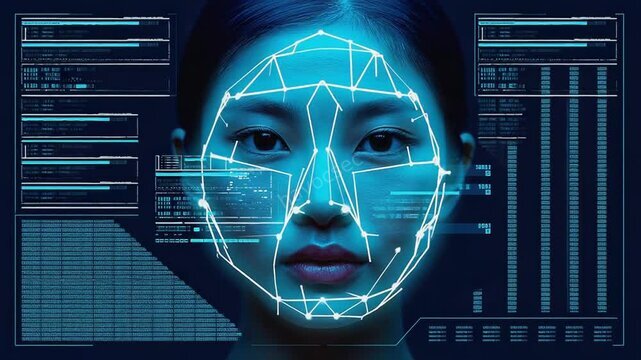
A single photograph fed into an AI image intelligence engine can return location data, device fingerprints, and cross-platform identity matches within seconds.
Part 3: Real Scenarios - AI OSINT in Action
Scenario 1: The Phishing Campaign That Gave Itself Away
Context: A cybersecurity team at a bank received reports of phishing emails targeting employees. Classic setup - spoofed domain, credential-harvesting landing page.
The AI OSINT play:
-
Feedly Threat Intelligence was already monitoring dark web forums for mentions of the bank’s name. It flagged a post from 48 hours earlier where a threat actor was selling a “fresh phishing kit” targeting that exact institution.
-
The analyst fed the phishing domain into SpiderFoot. Within 3 minutes: the registrar, hosting provider, associated email (a burner Gmail), and - crucially - two other phishing domains registered from the same email on the same day.
-
Maltego was used to map the infrastructure. The three domains all resolved to the same bulletproof hosting provider in Eastern Europe. The hosting provider had been flagged in 14 previous phishing campaigns across the past year.
-
All three domains were blocked, the Gmail reported, and the hosting provider’s entire ASN range was added to the bank’s blocklist - before a single employee was phished.
Time taken: 47 minutes. Pre-AI equivalent: 2–3 analyst days.
Scenario 2: Identifying a Disinformation Actor
Context: A journalist was investigating a coordinated disinformation network spreading false health claims across social media platforms.
The AI OSINT play:
-
The journalist used Meltwater’s AI social listening to cluster accounts by behavior - posting frequency, message timing, language patterns, and content overlap. With Meltwater, OSINT investigators can search, monitor, and analyze billions of conversations across a multitude of platforms to understand public sentiment and track emerging issues.
-
The clustering algorithm identified 47 accounts that behaved identically - posting the same content within seconds of each other, all created in the same 72-hour window.
-
Reverse image search on profile photos (via Lenso.ai) revealed that 31 of the 47 profile pictures were AI-generated faces - not real people.
-
theHarvester was used against the one domain linked across several bios, revealing a web of interconnected infrastructure.
Result: The journalist published a documented investigation of a 47-account bot network with full evidence chain - something that previously required weeks of manual correlation.
Scenario 3: Missing Person Investigation
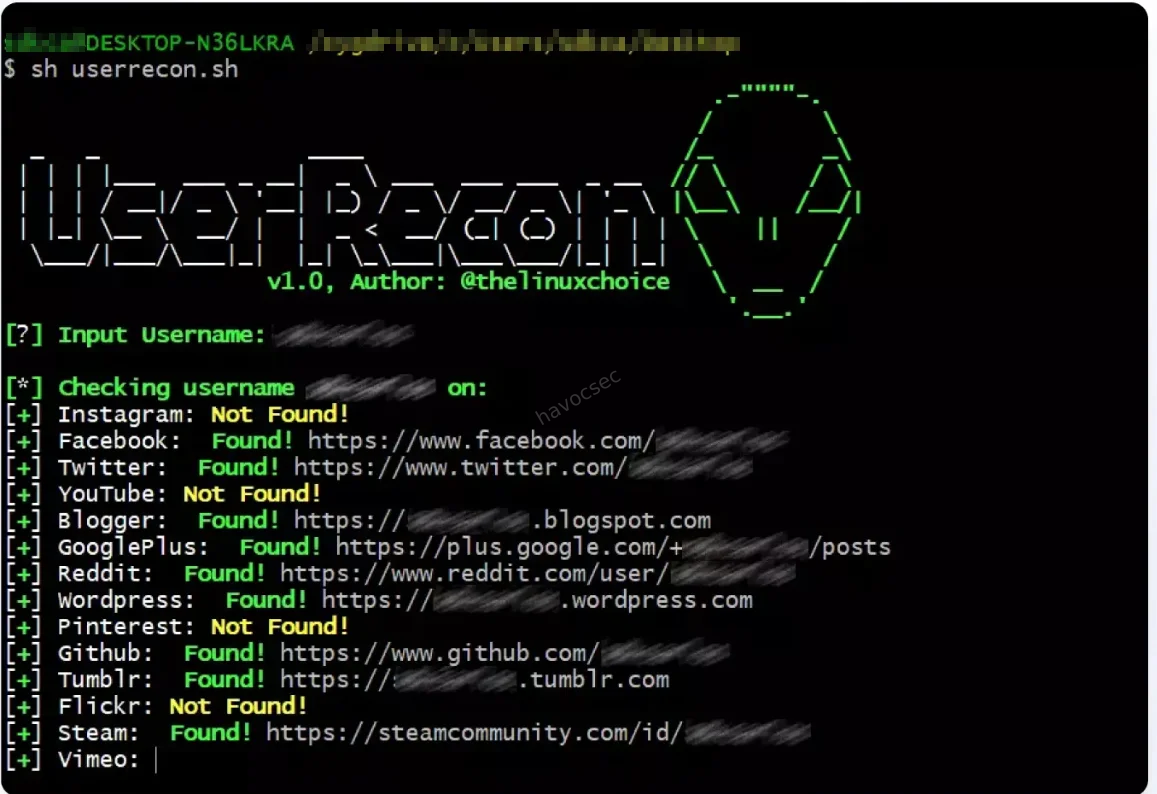
Context: A family asked a private investigator to locate an adult who had gone off-grid. Last known username: r3dph0enix_88.
The AI OSINT play:
Step 1 — Run the username through Sherlock and WhatsMyName:
sherlock r3dph0enix_88 --output results.txt
# Returns: active on Reddit, DeviantArt, an old gaming forum,
# and a fitness tracking appStep 2 - The fitness app profile was public and contained location-tagged run routes - a neighborhood in a specific city.
Step 3 - The Reddit account had posts mentioning a specific gym and a local coffee shop by name.
Step 4 - The DeviantArt portfolio contained artwork uploaded over 6 years. EXIF metadata on the earliest images (pre-2020, before smartphones stripped GPS data) contained GPS coordinates of a home address.
Step 5 - Cross-referenced address with public records. Confirmed identity.
The AI contribution: AI and ML have the power to analyze data at a super fast scale - they are huge time-saving tools that free up analysts to focus on analysis rather than collection. The EXIF extraction, cross-platform correlation, and public record lookup were all automated. The investigator’s role was judgment and interpretation - not data collection.
Part 4: The Ethical & Legal Lines
AI-powered OSINT is extraordinarily capable. That power demands discipline.
What’s Legal (Generally)
- Collecting publicly posted information (social media, forums, public records)
- Running username lookups on platforms that display public profiles
- Using reverse image search on images that were publicly shared
- Monitoring public-facing web infrastructure (Shodan, Censys)
What Gets Gray Fast
- Aggregating individually public data points into a comprehensive personal profile (may trigger GDPR, CCPA depending on jurisdiction)
- Facial recognition on images scraped without consent
- Cross-referencing breach databases — legal for defenders, questionable for others
- Any investigation targeting a private individual without a legitimate purpose
The Investigator’s Rule
Always ask: does my method of collection match the purpose of the investigation? Law enforcement, journalists, and security professionals operate under different legal and ethical frameworks. Know yours before you run a tool.
While AI brings speed, scalability, and precision to OSINT, ethical considerations, misinformation detection, and AI model accuracy remain critical concerns.
Part 5: Where AI OSINT Is Heading Next
The current trajectory points clearly toward:
Fully autonomous investigation pipelines - where an analyst submits a single seed (an email, a username, a phone number) and receives a complete, structured intelligence report with confidence scores, source citations, and relationship maps. No manual steps.
Deepfake detection as standard - AI can analyze video or audio files for signs of deepfakes by detecting subtle signs of manipulation through facial movements, audio inconsistencies, and pixel patterns. By 2027, every major OSINT platform will have deepfake flagging built in.
Real-time dark web monitoring - AI that continuously scans dark web forums, paste sites, and encrypted chat channels and alerts investigators to relevant intelligence as it appears - not hours later.
Predictive threat modeling - Systems that don’t just describe threats, but forecast them based on behavioral signatures in public data. Tools like MiroFish are already doing this with swarm simulation: feed it a threat actor’s known behavior patterns and a triggering event, and it returns a probabilistic forecast of their next move - modeled through thousands of interacting AI agents that simulate real human behavior at scale. This class of tool will be standard in serious threat intelligence teams by 2028.
Where applicable, incorporating AI and ML into OSINT operations ensures that teams remain at the forefront of technology, adapting to the evolving landscape of intelligence gathering.
Key Takeaways
- AI hasn’t replaced OSINT investigators - it has eliminated the grunt work so humans can focus on judgment, interpretation, and ethics
- Maltego, SpiderFoot, Shodan, Recorded Future, and MiroFish are the five pillars of AI-enhanced OSINT in 2026
- NLP, computer vision, entity resolution, and swarm simulation are the four ML capabilities driving the biggest changes
- MiroFish bridges the temporal gap - traditional OSINT covers the past and present; swarm prediction engines model the future
- Prompt engineering is now an OSINT skill - knowing how to ask AI tools the right questions is as important as knowing which tools exist
- Legality ≠ ethicality - just because AI can aggregate a full profile on someone doesn’t mean every context makes that appropriate
- The OSINT market is exploding - understanding AI-powered tools is no longer optional for professionals in security, journalism, or investigations
Have a real OSINT scenario you’ve tackled with AI tools? Drop it in the comments — this community learns best from real cases.
SEO Keywords: AI OSINT 2026, machine learning intelligence gathering, automated OSINT tools, Maltego SpiderFoot Shodan, AI cybersecurity investigation, NLP OSINT, facial recognition OSINT, open source intelligence AI, threat intelligence ML, MiroFish swarm intelligence OSINT, predictive threat modeling, multi-agent simulation intelligence



Comments